

Custom Search
|
|

|
||
 MIL-HDBK-1013/12
decisions and provide supporting information also simplify the
procedure.
D-1.2.1
Required Information. The following information is
required for the planning procedure:
a) Worksheets (see Appendix B):
1) None
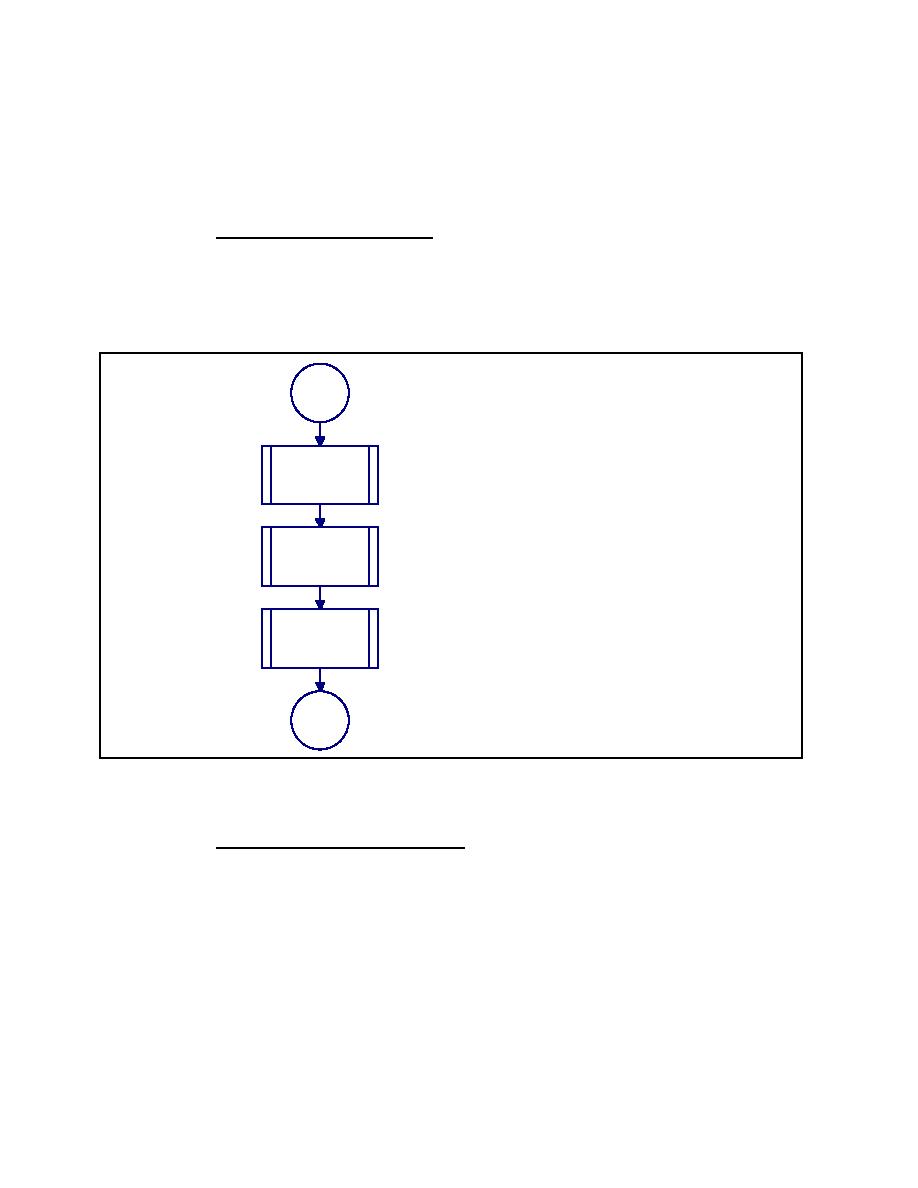
<1> Assets. Identify and categorize
assets using Figure D-3. Proceed
Start
to <2>.
<2> Design Basis Threat. Identify
aggressors and likely tactics using
Figure D-9. Proceed to <3>
<3> Level of Protection. Determine
<1> Assets
level of protection for each
applicable tactic for each asset
using level of protection procedure
described in Figure D-20. Stop
planning procedure.
<2> Design
Basis Threat
<3> Level Of
Protection
Stop
Figure D-2
Process Chart and Description:
Planning Procedure
D-1.2.2
Information Sensitivity. Information generated as
output from the planning procedure indicates the assets the user
considers important and the threats against which the protective
system is designed. This is sensitive information and will be
treated as "For Official Use Only" as a minimum. This applies to
completed worksheets and to other documentation which reflects
the sensitive information on the worksheets. The information
will be considered for classification at an appropriate level
when either of the following criteria exist:
171
|
 
|
|
 |
||